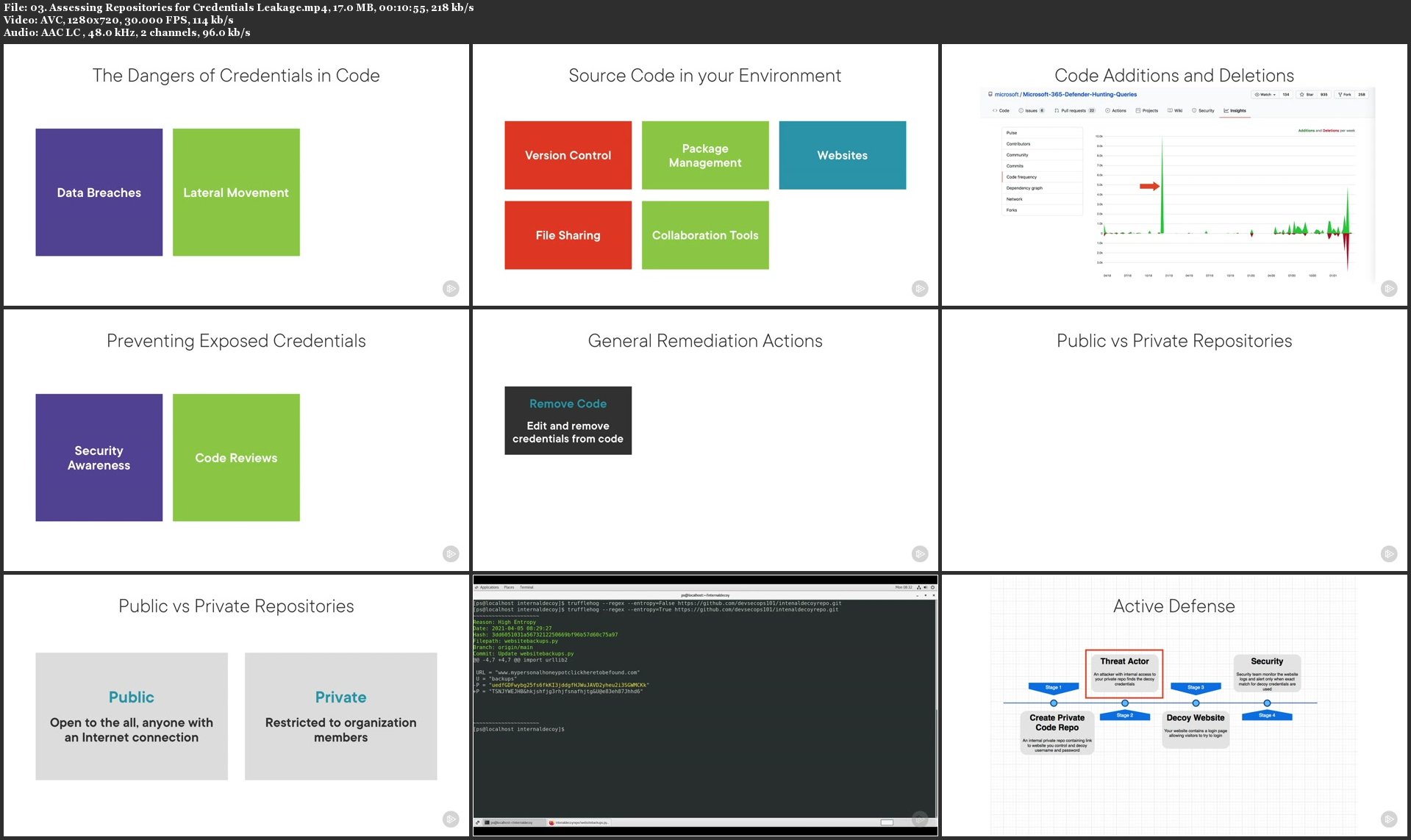
File Analysis with TruffleHog
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 23m | 42.8 MB
Instructor: Tim Coakley
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 23m | 42.8 MB
Instructor: Tim Coakley
In this course, you will learn to perform file analysis of source code repositories using the tool TruffleHog, which is one of the essential steps of continuous data loss detection and prevention
In this course, File Analysis with TruffleHog you will cover how to utilize TruffleHog to identify and detect sensitive data such as credentials accidentally committed to source code repository environments. You will discover how to audit your source environments including recent and historic source code commits. You will learn how to place decoy credentials in source code repositories and analyze your repositories for exposed credentials. When you are finished with this course, you will have the skills and knowledge to aid in mitigating technique T1552 using TruffleHog.